Are you looking to enhance your understanding of data trustworthiness in cloud services? In this comprehensive guide, we will delve into the crucial aspects of data security, privacy, governance, and compliance within cloud environments. As organizations increasingly rely on cloud services for data storage and processing, the importance of ensuring Cloud service data trustworthiness cannot be overstated. Stay tuned to discover best practices for establishing and maintaining trust in your cloud data.
Understanding the Essence of Data Trustworthiness in Cloud Services
In the realm of cloud services, data trustworthiness embodies the essence of reliable, accurate, and integral data storage and processing. For businesses, establishing trust in cloud data is paramount, enabling informed decision-making and upholding data integrity vital for operations. Key contributors to data trustworthiness encompass data security, privacy, governance, and compliance, shaping the foundation of a secure data ecosystem.
Evaluation of cloud providers ensues as a crucial step for organizations, where scrutinizing the provider’s adherence to data security, privacy, governance, and compliance standards is imperative. Prioritizing these fundamental factors before entrusting sensitive data to a cloud service provider serves as a proactive measure in safeguarding data trustworthiness. Striving for transparency and alignment with organizational data values paves the way for a trustworthy cloud data environment.
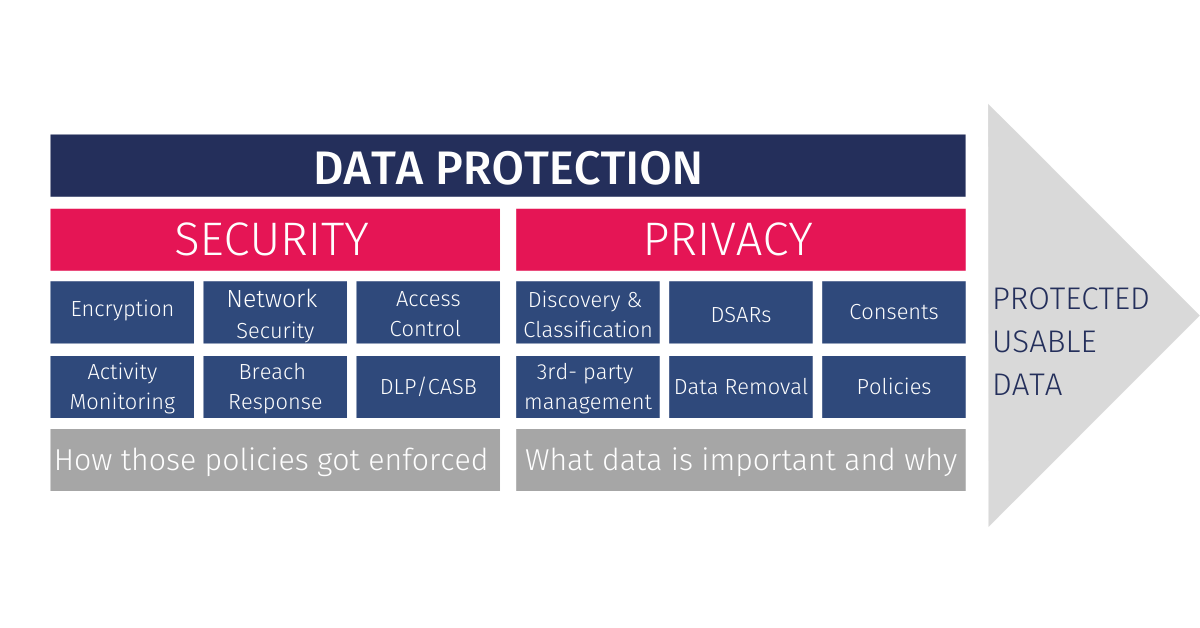
By emphasizing data trustworthiness in cloud services, businesses can fortify their data assets against threats, ensuring the integrity and reliability necessary for seamless operations. The convergence of robust data security measures, stringent data privacy protocols, effective data governance frameworks, and meticulous data compliance practices cultivates a holistic approach to nurturing and preserving data trustworthiness. Organizations poised to leverage these critical elements set the stage for a resilient and sustainable cloud data architecture.
Ensuring Data Security in Cloud Services
Data security in cloud services is paramount to safeguarding data from unauthorized access, theft, or damage. Cloud providers employ robust security measures like encryption, access controls, and intrusion detection systems to fortify data protection. Organizations must meticulously evaluate these security controls to align with their specific security prerequisites. Conducting routine security audits and penetration testing aids in pinpointing and rectifying probable vulnerabilities, ensuring a robust defense against potential security breaches in cloud environments.

Safeguarding Data Privacy in Cloud Services
When it comes to Data Trustworthiness in Cloud Services, adhering to data privacy regulations is paramount. These regulations dictate how personal data is managed, necessitating cloud providers to uphold strict compliance to safeguard user privacy. Organizations must verify that their chosen cloud providers implement robust data privacy protocols. Employing data anonymization and pseudonymization techniques adds an extra layer of protection for sensitive personal data, ensuring privacy is maintained within the cloud environment.

Evaluating Cloud Providers for Data Trustworthiness
Organizations seeking to ensure data trustworthiness in cloud services must prioritize rigorous due diligence. When evaluating cloud providers, scrutinize their security protocols, privacy policies, governance standards, and adherence to compliance regulations. Requesting security whitepapers, privacy impact assessments, and compliance reports is essential to gain a deeper understanding of their data protection mechanisms. Additionally, leveraging third-party audits and industry analyst evaluations offers unbiased insights into a provider’s trustworthiness and reliability.

Enhancing Data Trustworthiness in Cloud Services
When it comes to enhancing data trustworthiness in cloud services, implementing robust data encryption measures is paramount. Encrypting data both in transit and at rest adds an extra layer of security, safeguarding sensitive information from unauthorized access. This practice ensures that data remains protected, maintaining its integrity and confidentiality, thereby upholding data trustworthiness in cloud services.
Moreover, establishing clear data access policies and enforcing role-based access controls are essential steps in bolstering data trustworthiness. By defining who has access to specific data based on roles and responsibilities, organizations can limit the risk of data breaches and unauthorized usage. This approach enhances data security and fosters a culture of trust within the cloud environment, promoting data trustworthiness in cloud services.
Regularly monitoring and auditing cloud data access logs play a crucial role in maintaining data trustworthiness. By tracking and analyzing data access activities, organizations can swiftly identify any anomalies or suspicious behavior, enabling timely intervention to prevent potential security threats. This proactive measure enhances data transparency and accountability, ensuring the overall integrity of cloud-stored data and elevating data trustworthiness.
Additionally, leveraging data backup and recovery services is a fundamental best practice for enhancing data trustworthiness in cloud services. By implementing reliable backup solutions, organizations can mitigate the risks associated with data loss due to system failures, cyber-attacks, or natural disasters. This proactive approach not only ensures data availability and continuity but also reinforces data integrity, strengthening the overall trustworthiness of data stored in cloud environments.

